It has been almost a year since VMware introduced the Hybrid Linked Mode (HLM) capability, which provides customers with a consistent operating experience for managing and consuming resources from both their on-premises and VMware Cloud on AWS (VMC) environments. Feedback from customers on HLM has been fantastic, especially when new or prospective VMC customers learn about HLM for the very first time. Customers were pleasantly surprised at how seamless the experience was when consuming VMC resources, using a familiar interface, the vSphere UI.
Here is a quick recap of what HLM provides today:
- HLM allows customers to link a single VMC instance to a single on-prem SSO Domain which can contain one or more vCenter Servers (Enhanced Linked Mode) while maintaining separate administrative domains (e.g. on-prem user is Administrator while VMC user is CloudAdmin only)
- SSO Domains will be different between on-prem and VMC, however it is a 1:1 relationship
- A trust is established where the on-prem vCenter Server trusts the incoming connections from VMC as they share the same Active Directory identity source. Data is sync'ed uni-directionally from on-prem to VMC
- Can be configured at any point in the on-prem vCenter Server lifecycle, no restrictions to initial install and can easily be un-linked unlike ELM
- Both Embedded & External vCenter Server deployments are supported
- HLM supports different versions of vCenter Server between on-prem (6.5d+) and VMC, especially as VMC will almost always run a newer version of vSphere
- Users MUST login to VMC vCenter Server for single-pane of glass management (H5 Client supported only), logging into on-prem vCenter Server will NOT show VMC vCenter Server
- Roles are NOT replicated due to the restrictive access model in VMC
One of the benefits with HLM being delivered as part of the VMC Service is that the team is able to continuously deliver improvements to how HLM functions. An area that the HLM team has been focusing on based on customer feedback is how customers actually consume HLM. Today, customers must login to the vSphere UI of the VMC vCenter Server to get the benefits of HLM. If you login to your on-prem vCenter Server (which is part of the HLM configuration), the VMC vCenter Server is not available as the on-prem vSphere UI is not aware of HLM. Not only can this nuance be easily forgotten, but customers are usually logged into their on-prem infrastructure when performing operations locally. Furthermore, depending on your external network connectivity, you could potentially incur unnecessary latency when performing operations that are intended only for your on-prem vCenter Server as you must traverse through the VMC vCenter Server and then back into your on-prem environment.
UPDATE (10/09/18) - Here is a recent webinar on vCenter Cloud Gateway which was given by one of our Customer Success Engineers, Eric Huber
vCenter Cloud Gateway
To help solve some of these challenges and provides a more seamless hybrid cloud experience, the HLM team has been working on a new vCenter Cloud Gateway (VCG) appliance, which has also been updated in the latest VMC 1.5 release. Unlike the current HLM workflow which is configured and initiated from the VMC vCenter Server vSphere UI, the new VCG appliance allows customers to enable and consume HLM directly from their on-prem vCenter Server. The VCG includes the vSphere UI interface and customers would use that UI to manage both their on-prem vCenter Server as well as the VMC vCenter Server. The VCG experience is exactly the same as the HLM experience today, with the exception that it is now running locally in you on-prem environment.
Note: Customers can still configure HLM using the current method which is initiated from the VMC vCenter Server. However it is important to note that which ever method is used, the vCenter Server in that environment must be used to consume HLM as it is not a bi-directional configuration.
From a network connectivity standpoint, the requirements have also been greatly simplified and the only outbound connectivity that is now required is between the VCG and the VMC vCenter Server. Previously, the VMC vCenter Server would also require network access to customers Active Directory as well as the credentials to add a new identity source to the VMC vCenter Server, which not all customers were comfortable with. With the VCG running in your on-prem environment, access to these infrastructure services can now be managed and secured based on your corporate security policies. Latency is also no longer a concern when performing operations intended for the on-prem environment as everything is now local and initiated from the on-prem vCenter Server, instead of the VMC vCenter Server. Obviously, if you have a high latency external network connection, accessing the VMC vCenter Server from your on-prem vCenter Server can still be affected.
There are some additional benefits to the VCG that may not be immediately apparent. If you recall earlier, I had mentioned that HLM is delivered as part of the VMC Service, this also means that VMC is responsible for the full lifecycle management (patch/upgrade/backup/monitor) of the VCG within a customers environment. Historically, customers would be responsible for managing any on-prem deployments, but VMC is a service and the VCG is merely an extension of that service. As VMC provides new software bundles within the SDDC, this will also include updates to the VCG. Customers will be notified through the VMC Console for updates and in the future this will include notifications directly in the VCG itself.
Lastly, because the VCG includes the vSphere UI, customers automatically benefit from getting access to the latest VMC version of the vSphere HTML5 Client that is fully interoperable with a customers existing on-prem environment. For customers who may not be running the latest version of vSphere in their on-prem environment, you now have access to all the new features as well as enhancements made to the vSphere UI without having to modify your existing vCenter Server which is a huge plus in my opinion, especially with some of the enhanced H5 workflows which will be even newer than what we are shipping currently.
Deploying vCenter Cloud Gateway
Step 1 - Download and deploy the VCG appliance into your on-prem infrastructure. The download comes in the form of an ISO, similiar to that of the VCSA. Once extracted or mounted, the contents includes both a UI and CLI Installer which should be familiar for those who have deployed a VCSA.
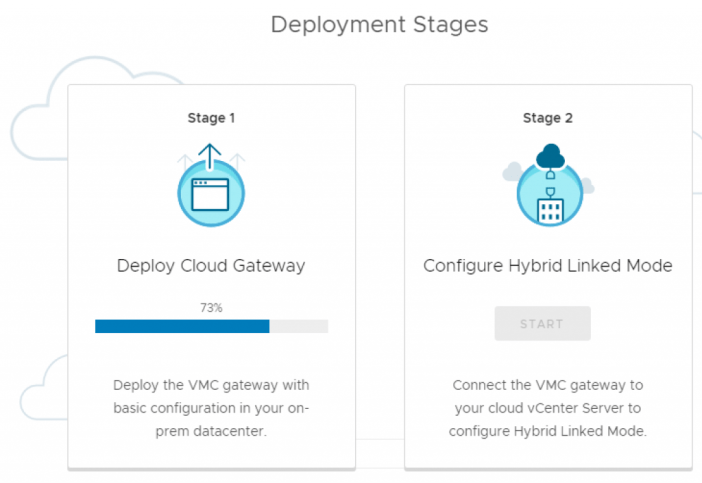
Similarly to the VCSA installation, there are two Stages to the deployment. Stage 1 deploys the OVA and associates VCG with the given vCenter Server and your SSO Domain. In, Stage 2 the actual linking to form the HLM is then configured. If the on-prem vCenter Server that are you adding to HLM is configured with Active Directory over LDAP, then you can simply begin Stage 2 when it is ready. However, if you are using Integrated Windows Authentication (IWA), then you need to close the Installer after Stage 1 and perform an additional step before you can setup HML (see Step 2 below)
UPDATE (01/01/19) - Active Directory integration is now part of the VCG Stage 1 Installer UI as well as CLI. You no longer need to manually join the appliance to Active Directory separately and Step 2 below is no longer needed if you are using the latest version found on VMware's site.
Step 2 - We need to join the VCG appliance to your Active Directory Domain if you are using IWA for your on-prem vCenter Server. Currently, you need to use the domainjoin-cli tool and detailed instructions can be found in the VMC documentation here. We are definitely looking to improve the installer in the future to also include the ability to join Active Directory within the UI and CLI, so this additional step will not be required in the future for customers using IWA.
Step 3 - Once the VCG has joined your Active Directory Domain, open a browser to the Hostname/IP Address of your VCG appliance. You can now login using the same credentials you would to your on-prem vCenter Server. Click on the Menu at the top and navigate to Administration->Hybrid Cloud->Linked Domains to configure HLM.
Next, you will provide your VMC vCenter Server information and credentials and the Active Directory group(s) you wish to link to the VMC's Cloud Administrator group for accessing the VMC vCenter Server. Finally, click on Link to perform the HLM configuration.

If everything was successful, you will get a message asking you to log back into the vSphere UI. Once you do, you should now see both the inventory of your on-prem vCenter Server (which could include other vCenter Servers if it is part of an Enhanced Linked Mode) as well as the VMC vCenter Server as shown in the screenshot below.

If you wish to remove HLM, simply return to the "Linked Domains" and click on the Unlink option. You can also update the Cloud Admins groups to either add or remove a group in this same view.

I think the VCG definitely opens up the door for some interesting hybrid cloud experiences in the future. What capabilities or features would you be interested in seeing?

Thanks for the comment!